Smart Phone Remote Controller ● Widespread Compatibility: Your smartphone can function effectively with the standard connector that is frequently used to replace iOS cellphones.● Plug and Play: Your smartphone may become an…
Configure Cisco Named Extended Access Control List
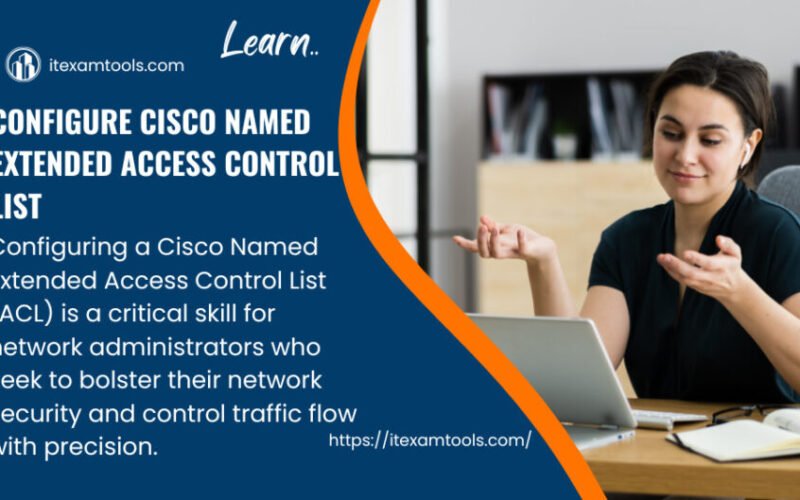
In this article will demonstrate on extended named access control List (Extended Named ACL).
Configuring a Cisco Named Extended Access Control List (ACL) is a critical skill for network administrators who seek to bolster their network security and control traffic flow with precision.
Unlike standard ACLs, named extended ACLs offer greater flexibility and ease of management. These ACLs are comprised of access control entries that define the rules governing traffic based on source and destination IP addresses, protocols, and port numbers.
By using meaningful names for these ACLs, administrators can quickly identify their purpose, enhancing network clarity and maintainability.
To configure a Cisco Extended Access Control, the first step involves creating the list with a descriptive name, such as “ACL_WEBSERVERS.” Once defined, the network administrator proceeds to specify the access control entries, which dictate the permitted or denied traffic attributes.
For instance, consider a scenario where a company wants to allow SSH traffic (TCP port 22) from a specific subnet (192.168.1.0/24) to their web servers (10.0.0.1 and 10.0.0.2) only. The named extended ACL would look as follows:

arduino
ip access-list extended ACL_WEBSERVERS
permit tcp 192.168.1.0 0.0.0.255 host 10.0.0.1 eq 22
permit tcp 192.168.1.0 0.0.0.255 host 10.0.0.2 eq 22
deny ip any any
In this example, the first two lines permit SSH traffic from the specified subnet to the designated web servers, while the final line denies any other traffic not explicitly permitted. Once configured, the ACL must be applied to the appropriate interface using the “ip access-group” command:
kotlin
interface GigabitEthernet0/0
ip access-group ACL_WEBSERVERS in
By thoughtfully implementing named extended ACLs, network administrators can effectively protect their networks from unauthorized access and control the flow of traffic with precision, safeguarding sensitive resources and enhancing overall network security.
————————————————-
Access control list is used for filtering unwanted traffic, there are two types of acl :numbered and named acl. numbered access lists are either standard or extended. Also, named access lists are either standard or extended. So, there are four access lists
- Numbered standard access list
- Numbered extended access list
- Named standard access list
- Named extended access list
In this article will cover Named Extended Access List. Extended means it will filter the packet based on the source ip address, destination ip address, protocol, and port. Named means that the access list is identified by name not by number and has a feature of editing (adding and removing specific lines capability).
Access Control List Rules (Cisco Extended Access Control)
1- If you use Numbered (Standard and Extended) and Named (Standard and Extended) Access Lists, the packet is always compared with each line of the access list in sequential order, means If the source packet ip address matches the first line(entry) of the acl, the router will not check all other entries in the access list.
If the source ip address doesn’t match the first line of the acl, the router will check the second line and so on.
The packet is compared with lines of the access list only until a match is made. Once it matches the condition on a line of the access list, no further comparisons take place.
2- There is an implicit deny at the end of each access list—this means that if a packet doesn’t match the condition on any of the lines in the access list, the packet will be discarded.
3- The access list is applied on an interface in a specific direction -Inbound or Outbound. Inbound: The packets will be processed through the acl before routed to the outbound interfaces. Outbound: The packets are routed to the outbound interface, and then processed through the acl.

4- Standard (numbered and named) access control lists filter network traffic by examining the source ip address in a packet (filtering traffic based on the source ip address).
5- The Named Access Lists (Standard and Extended) are editable, means you can insert a line in between the lines or at the top of the entries. Also you can delete specific line. So, there is a capability of modifying the access list(adding a line or deleting specific line).
6- Standard Access Control List is placed as close to destination as possible.
7- Extended Access Control List is placed as close to source as possible.
Extended Named Access Lists (Cisco Extended Access Control)
Named Extended Access Control Lists use the following syntax
R(config)# ip access-list extended <access-list-name>
R(config-ext-nacl)<permit/deny> <protocol> < source address> <wildcard mask> <destination address> <wildcard mask><operator> <port>
[protocol]
| PROTOCOL | DESCRIPTION |
| ahp | Authentication Header Protocol |
| eigrp | Cisco’s EIGRP routing protocol |
| esp | Encapsulation Security Payload |
| gre | Cisco’s GRE tunneling |
| icmp | Internet Control Message Protocol |
| ip | Any Internet Protocol |
| ospf | OSPF routing protocol |
| tcp | Transmission Control Protocol |
| udp | User Datagram Protocol |
[operator]
| OPERATOR | DESCRIPTION |
| dscp | Match packets with given dscp value |
| eq | Match only packets on a given port number |
| established | established |
| gt | Match only packets with a greater port number |
| lt | Match only packets with a lower port number |
| neq | Match only packets not on a given port number |
| precedence | Match packets with given precedence value |
| range | Match only packets in the range of port numbers |
[port]
| PORT | DESCRIPTION |
| Port number | |
| ftp | File Transfer Protocol (21) |
| pop3 | Post Office Protocol v3 (110) |
| smtp | Simple Mail Transport Protocol (25) |
| telnet | Telnet (23) |
| www | World Wide Web (HTTP, 80) |
Looking at the above diagram, we want preventing network 192.168.10.0/24 from accessing network 192.168.30.0/24 using icmp-echo (ping) and ftp only, and everything else is permitted.
The extended access list is applied as close to source network, and we want preventing network 192.168.10.0/24 (Source) from accessing network 192.168.30.0/24(Destination) using icmp-echo and ftp. That’s why i will write the configuration on Router0.
Configuration Steps:
1- Create an access list
1-Router0(config)#ip access-list extended tariq
2-Router0(config-ext-nacl)# deny icmp 192.168.10.0 0.0.0.255 192.168.30.0 0.0.0.255 echo
3-Router0(config-ext-nacl)# deny tcp 192.168.10.0 0.0.0.255 192.168.30.0 0.0.0.255 eq 21
4-Router0(config-ext-nacl)# permit ip any any
Line 1:creating extended named access list, and tariq is the name of the access-list Line2:denying echo(ping) from the source network 192.168.10.0/24 to the destination network 192.168.30.0/24, echo is an application of the icmp protocol
Line3:denying ftp from the source network 192.168.10.0/24 to the destination network 192.168.30.0/24, ftp uses tcp.
Line4:permitting any protocol (ip means any protocol) from any source network to destination network, this means permitting everything.
2- The access list is applied on an interface in a specific direction: no action (permit or deny) will be taken until the access list is applied on an interface in a specific direction.
In this example we will apply the acl on the interface f0/0 in inbound direction, means the router interface g0/0 will receive the icmp-echo and ftp packets from network 192.168.10.0/24 that are going to network 192.168.30.0/24 and prevent these packets from being routed to the other interfaces such as s0/0/0.
So it blocks network 192.168.10.0/24 from reaching network 192.168.30.0/24 using the icmp-echo(ping) and ftp.
before writing the commands below, host 192.168.10.2 can ping to 192.168.30.2
Router0(config)#int f0/0
Router0(config-if)#ip access-group tariq in
After writing the above commands (applying the acl on the interface), host 192.168.10.2 can’t ping to 192.168.30.2
To edit this named access listhttps://youtu.be/RToV6h2rGeM
To view the configured access list
Router#sh access-lists
Extended IP access list tariq
10 deny icmp 192.168.10.0 0.0.0.255 192.168.30.0 0.0.0.255 echo (4 match(es))
20 deny tcp 192.168.10.0 0.0.0.255 192.168.30.0 0.0.0.255 eq ftp
30 permit ip any any (4 match(es))

Learn more..
Cisco Wireless Network Types
Learn Cisco Subnet Mask
Cisco OSPF Basic Configuration
Boost Your IT Career with The Ultimate MySQL Bootcamp
21 latest and most probable interview questions with answer for SOC analyst
Premium NetApp ONTAP Storage Complete course